Introduction:
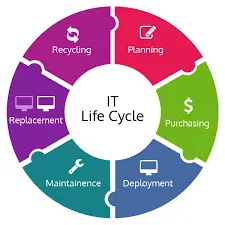
In the dynamic landscape of technology, businesses rely heavily on their IT infrastructure to drive innovation, enhance productivity, and stay competitive. However, managing the entire lifecycle of IT assets efficiently is no small feat. This is where IT Lifecycle Management (ITLM) comes into play. In this article, we will explore the key components and benefits of it lifecycle management process, shedding light on how organizations can optimize their IT investments.
Understanding IT Lifecycle Management:
IT Lifecycle Management is a strategic approach that involves planning, acquiring, deploying, maintaining, and eventually retiring IT assets within an organization. This holistic process helps businesses make informed decisions about their technology investments, ensuring optimal performance, security, and cost-effectiveness throughout the entire lifecycle of IT assets.
Key Components of IT Lifecycle Management:
- Planning and Procurement:
- Identify business needs and align IT strategies with organizational goals.
- Evaluate current IT infrastructure and plan for future requirements.
- Develop a comprehensive procurement strategy that considers both short-term and long-term needs.
- Deployment:
- Efficiently integrate new technologies into existing systems.
- Conduct thorough testing to ensure compatibility and performance.
- Provide training and support for end-users to maximize adoption and minimize disruptions.
- Management and Maintenance:
- Implement proactive monitoring to identify potential issues before they impact operations.
- Regularly update and patch software to enhance security and performance.
- Establish a robust system for asset tracking and inventory management.
- Optimization:
- Conduct regular performance reviews and optimizations to ensure maximum efficiency.
- Explore opportunities for technology upgrades or replacements to stay current with industry standards.
- Implement best practices to minimize downtime and maximize productivity.
- Security:
- Integrate security measures throughout the lifecycle, from procurement to retirement.
- Regularly update security protocols and educate users on cybersecurity best practices.
- Implement risk management strategies to mitigate potential threats.
- Retirement and Disposal:
- Develop a systematic approach to retiring outdated or obsolete technology.
- Ensure data security during the decommissioning process.
- Responsibly dispose of hardware following environmental regulations.
Also Read: Potential and Updated Uses of Face Recognition Technology in 2024
Benefits of IT Lifecycle Management:
- Cost Savings:
- Optimize resource allocation and reduce unnecessary expenditures.
- Minimize the risk of unexpected costs associated with outdated or unsupported technologies.
- Improved Productivity:
- Ensure that technology aligns with business objectives, boosting overall productivity.
- Minimize disruptions through proactive maintenance and support.
- Enhanced Security:
- Implement a comprehensive security strategy throughout the IT asset lifecycle.
- Stay ahead of potential cybersecurity threats with regular updates and risk assessments.
- Strategic Planning:
- Align IT investments with long-term organizational goals.
- Foster innovation by adopting emerging technologies that support business objectives.
Conclusion:
In the ever-evolving landscape of technology, IT Lifecycle Management is a crucial framework for organizations seeking to harness the full potential of their IT investments. By adopting a strategic and holistic approach, businesses can streamline processes, enhance security, and ensure that their technology infrastructure remains a valuable asset throughout its lifecycle. As organizations continue to navigate the complexities of the digital age, a well-executed ITLM strategy becomes not only a best practice but a key driver of sustained success.
You May Also Like: OgyMogy best spy app for android: The Cliché In Spyware Monitoring Technology